Hardware-Backed Cryptography: How the Secure Enclave Powers UltraLocked's Forensic Resilience
Technical deep-dive into how UltraLocked leverages Apple's Secure Enclave for hardware-backed encryption, key derivation, and forensic-resistant file protection on iOS.
The Secure Enclave: Hardware-Backed Cryptographic Isolation in UltraLocked
Introduction
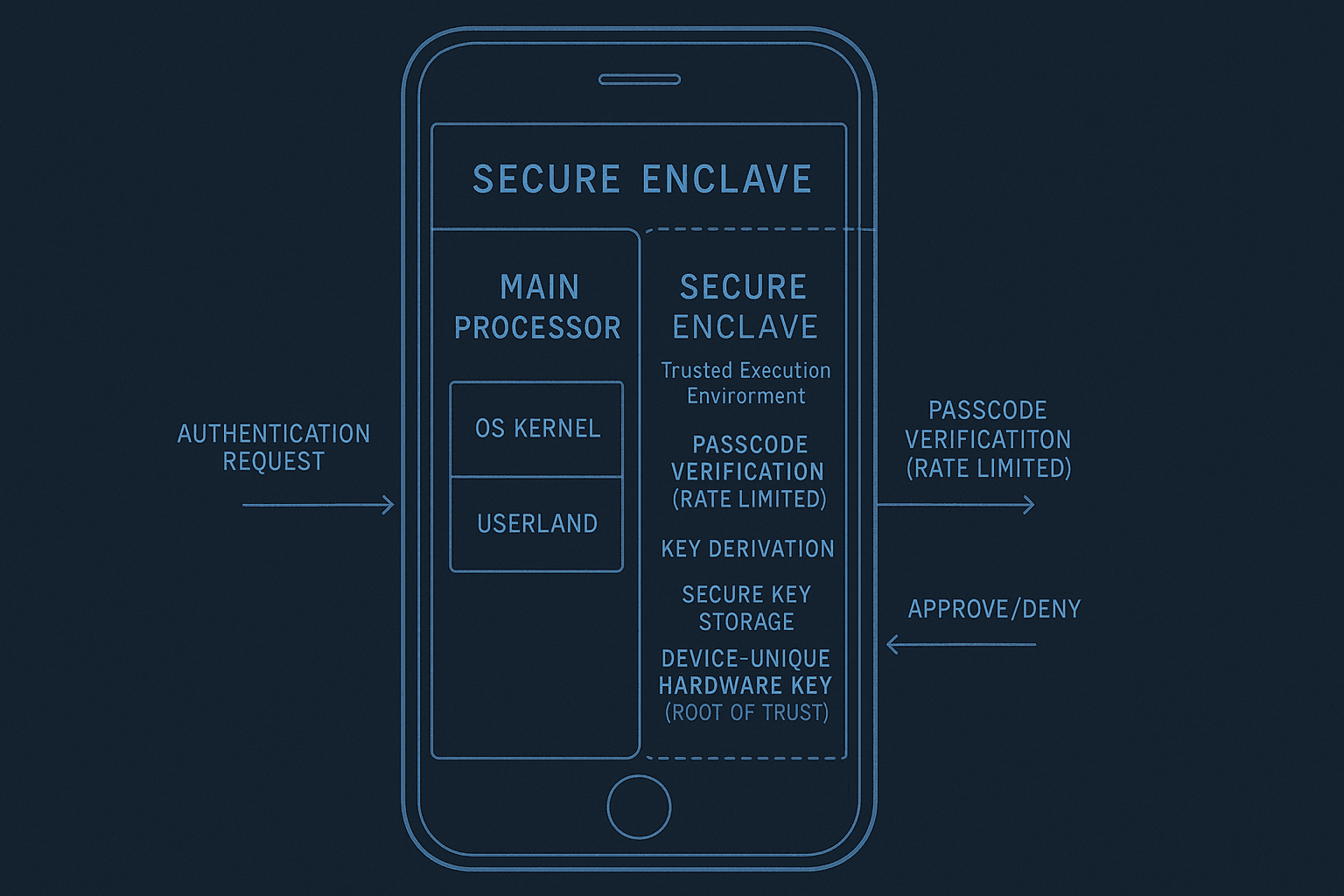
The Secure Enclave represents Apple's answer to a fundamental security problem: how do you perform sensitive cryptographic operations on a device you don't entirely control? Modern mobile operating systems sit in hostile territory. The kernel can be compromised. Userland processes can be memory-dumped. Debuggers can be attached. Forensic tools can extract live memory from a running device.
The Secure Enclave is a coprocessor embedded in Apple silicon—a hardware module physically separate from the main CPU—that executes cryptographic operations in isolation. Keys never leave the Secure Enclave unencrypted. Cryptographic material isn't exposed to the application layer, the operating system, or even debuggers. For UltraLocked, this isn't a convenience feature; it's the foundation of the entire architecture. If sensitive keys existed in userland memory, no amount of obfuscation or encryption would prevent an adversary with device access from extracting them.
This matters because most file encryption applications make a critical assumption: the operating system itself is trustworthy. UltraLocked doesn't. It offloads the assumption of trustworthiness to hardware that can't be patched remotely or compromised by a software exploit.
How It Works
UltraLocked leverages the Secure Enclave for all key derivation, encryption, and decryption operations. The flow looks like this:
Step 1: User Entry → Secure Enclave Request
When a user enters their PIN or biometric credential, the authentication happens in the Secure Enclave's trusted execution environment. The main OS never sees the raw credentials. Instead, the device makes a cryptographic commitment to the credential within the Secure Enclave and immediately discards the plaintext input.
Step 2: Key Derivation Inside the Enclave
The Secure Enclave derives encryption keys from the user's credential using PBKDF2 or equivalent key derivation functions. The derivation is deterministic but computationally expensive—it's deliberately slow. An attacker can't brute-force PINs by repeatedly calling the key derivation function outside the Secure Enclave because the derivation only happens inside the hardware-protected module. Rate-limiting and failed attempt lockouts are enforced by the Secure Enclave's internal state machine, not the application.
Step 3: Key Storage and Wrapping
Derived keys are wrapped with a hardware key bound to the device's secure storage. The Secure Enclave maintains this key in tamper-resistant memory. When the device is rebooted or locked, this key becomes inaccessible without passing biometric or PIN authentication again. The wrapped key can be stored in the application's sandbox or cloud backup without exposing the actual encryption key.
Step 4: Encryption and Decryption
When a user encrypts a file in UltraLocked, the file is transmitted to the Secure Enclave (or portions of it, to respect bandwidth limits). The Secure Enclave performs AES-256-GCM encryption or equivalent authenticated encryption using the derived key. The ciphertext returns to userland. The plaintext never exists in the application's memory—only the ciphertext does.
The same process reverses for decryption. Ciphertext goes in, the Secure Enclave decrypts it, and only the plaintext emerges (and only to the application that requested it).
Hardware Binding and Device-Specific Encryption
The Secure Enclave includes device-specific secrets that can't be extracted or replicated. When UltraLocked encrypts files, it can optionally bind encryption keys to these device secrets. This means a file encrypted on one iPhone literally cannot be decrypted on another iPhone, even with the correct PIN. The adversary would need both the PIN and physical possession of the original device.
This is distinct from software encryption, where an attacker with the password and ciphertext can brute-force offline. Here, the Secure Enclave enforces rate-limiting and authentication delays at the hardware level.
Biometric Integration Without Credential Storage
Biometric data (Face ID, Touch ID) is also processed by the Secure Enclave. UltraLocked never stores the biometric itself—only a biometric template used for matching. When a user authenticates with biometrics, the Secure Enclave compares the presented biometric against its stored template. If it matches, the Secure Enclave unlocks the wrapped keys. The template never leaves the Secure Enclave.
This prevents a compromise of the application from exposing biometric data. Even if an attacker gains full code execution in UltraLocked, they still can't extract face or fingerprint information because it never exists outside the Secure Enclave's boundaries.
Why UltraLocked Chose This Approach
This design prioritizes security over almost everything else. UltraLocked does not attempt to compete on speed. Performing all cryptographic operations in the Secure Enclave is slower than using optimized CPU instructions in userland. Key derivation is intentionally expensive. Biometric matching has latency. The user experiences a slight delay unlocking the vault.
UltraLocked accepts this trade-off because the adversary it defends against is not a script kiddie running off-the-shelf tools. It defends against forensic examiners, law enforcement, state actors, and sophisticated attackers with physical access to the device. Against these threats, speed is irrelevant. Security is the only metric.
Hardware binding creates another trade-off: inflexibility. A user can't easily migrate their vault to a new device by extracting the key. They must re-encrypt with new device-specific secrets. UltraLocked accepts this because the alternative—storing globally usable keys—would create a single point of failure. If the key is ever compromised, all backups and copies become vulnerable.
The Secure Enclave approach also sacrifices transparency. A developer can't audit Secure Enclave code because Apple doesn't publish it. Users must trust Apple's implementation. UltraLocked's team made this trust decision explicitly: Apple's Secure Enclave design and track record represent a better security posture than building custom cryptographic code in userland where it could be more easily compromised or audited by an attacker.
Finally, this approach limits functionality. The Secure Enclave is not a general-purpose processor. It can't run arbitrary code. UltraLocked must design around the Secure Enclave's constraints, not extend it. Features requiring complex computation must either happen outside the Secure Enclave (accepting reduced security) or be abandoned.
What It Protects Against
Forensic Decryption and Memory Extraction
An investigator with physical possession of an iPhone running UltraLocked cannot extract encryption keys from memory. Forensic tools that dump RAM don't yield keys—the keys are in the Secure Enclave and inaccessible to the OS. Even tools that extract live memory from a suspended or frozen device won't reveal keys because the Secure Enclave is a separate processor with its own memory hierarchy.
Brute-Force PIN Attacks
A common attack against encrypted containers: extract the wrapped key, then attempt offline password cracking on a high-performance GPU. UltraLocked's Secure Enclave rate-limits authentication attempts and enforces delays even in offline scenarios where the attacker has extracted the wrapped key material. The Secure Enclave's key derivation function can't be executed outside the hardware module, preventing parallel cracking.
Malware and Userland Compromise
If an attacker gains code execution in UltraLocked or the iOS system, they still can't decrypt the vault without passing Secure Enclave authentication. Biometric templates and derivation keys remain in the hardware-protected module. Malware can't hook cryptographic functions because the functions don't exist in userland.
Stolen or Lost Devices
A user who loses their iPhone doesn't lose the ability to remotely wipe their vault. More importantly, whoever finds the device faces a Secure Enclave that enforces authentication and rate-limiting. Without the PIN or valid biometric, brute-forcing is infeasible even with unlimited time and specialized equipment.
Key Replication Across Devices
Device-specific binding means a vault encrypted on one iPhone cannot be decrypted on another, even with the correct PIN. An attacker must compromise the specific device they want to access.
Limitations & Honest Caveats
The Secure Enclave provides hardware-level protection, but it's not invincible. An attacker with advanced laboratory equipment could attempt side-channel attacks on the Secure Enclave itself—timing attacks, power analysis, or other hardware-level exploits. These attacks are expensive and require specialized knowledge, but they're theoretically possible.
UltraLocked also relies on Apple's Secure Enclave implementation being correctly designed. A catastrophic flaw in the Secure Enclave's architecture or the hardware itself would break the security model. Users must implicitly trust Apple.
The Secure Enclave doesn't protect against coercion. If an adversary can force a user to provide their PIN or biometric, the vault becomes accessible. UltraLocked's emergency protocols mitigate this by allowing users to establish decoy vaults, but these are additional safeguards, not fundamental guarantees.
Finally, Secure Enclave protection is only available on devices with Apple's modern silicon (A-series processors or newer). Older iPhones with different processors may have older Secure Enclave implementations with different security properties. UltraLocked will run on these devices but with reduced cryptographic guarantees.
Conclusion
The Secure Enclave isn't a perfect solution, but it shifts the attack surface from software to hardware. Software exploits remain possible, but extracting encryption keys becomes orders of magnitude harder. This aligns with UltraLocked's zero-trust philosophy: assume the OS can be compromised, assume userland can be memory-dumped, and rely on hardware that can't be. Hardware-backed cryptographic isolation isn't new—it's standard in military hardware and HSMs—but bringing it to consumer iOS devices fundamentally changes what's possible for file encryption at rest and in motion. For users who need forensic resilience and plausible deniability, the Secure Enclave is the difference between theoretical encryption and practical protection.