Vercel Breach Exposes the Fragility of Cloud-Dependent Crypto Infrastructure
Vercel's breach via compromised AI tool exposed crypto API keys. Analysis of cloud dependency risks and why hardware-anchored, offline architecture matters.
Security insights, product updates, and tutorials from the UltraLocked team.
Vercel's breach via compromised AI tool exposed crypto API keys. Analysis of cloud dependency risks and why hardware-anchored, offline architecture matters.
When even FBI directors get hacked, professionals need hardware-secured, offline storage for sensitive files—not cloud accounts vulnerable to nation-states.

How journalists and activists use UltraLocked's Duress Code to protect sensitive sources during high-risk travel and border crossings. A real-world case study.
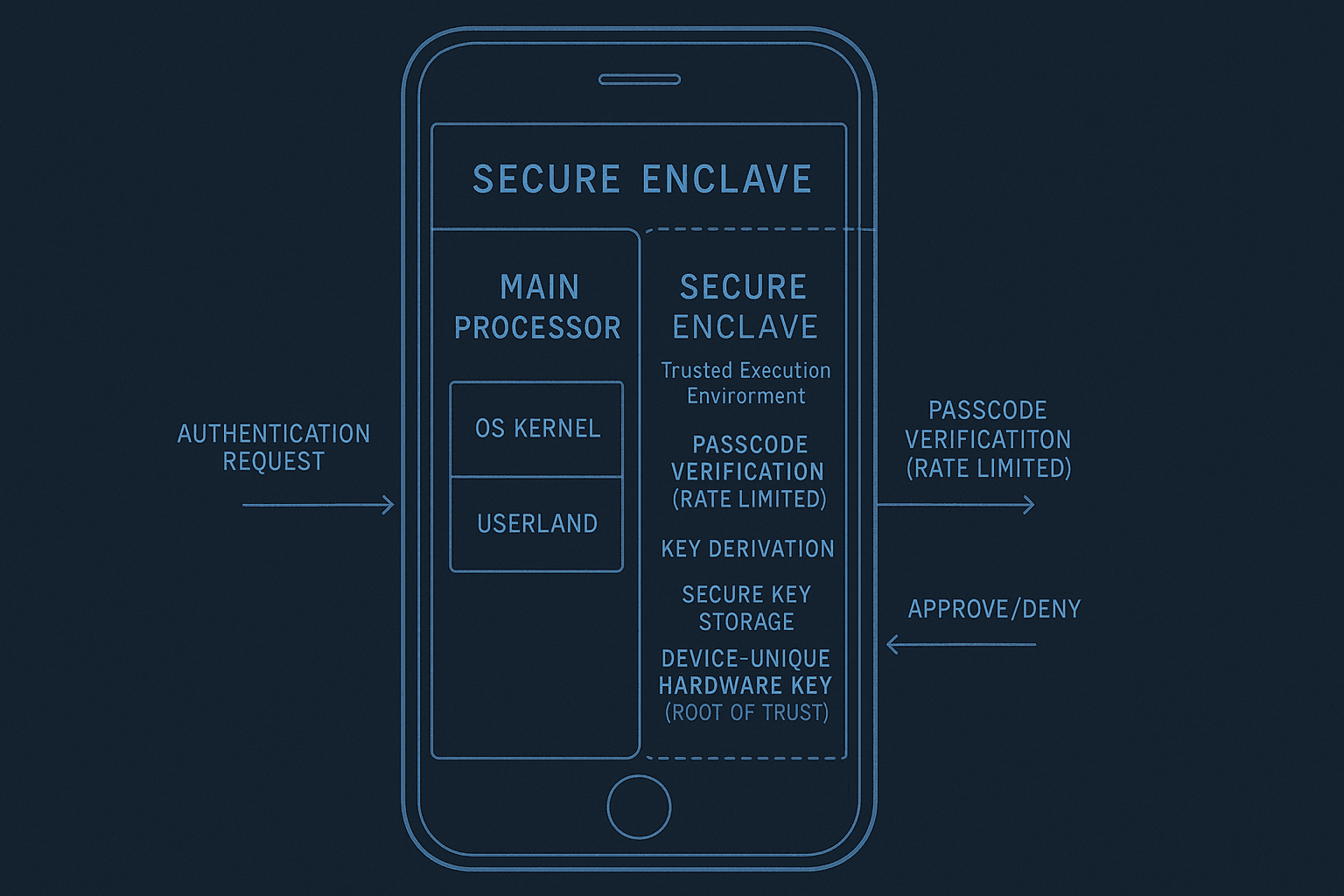
Technical deep-dive into how UltraLocked leverages Apple's Secure Enclave for hardware-backed encryption, key derivation, and forensic-resistant file protection on iOS.
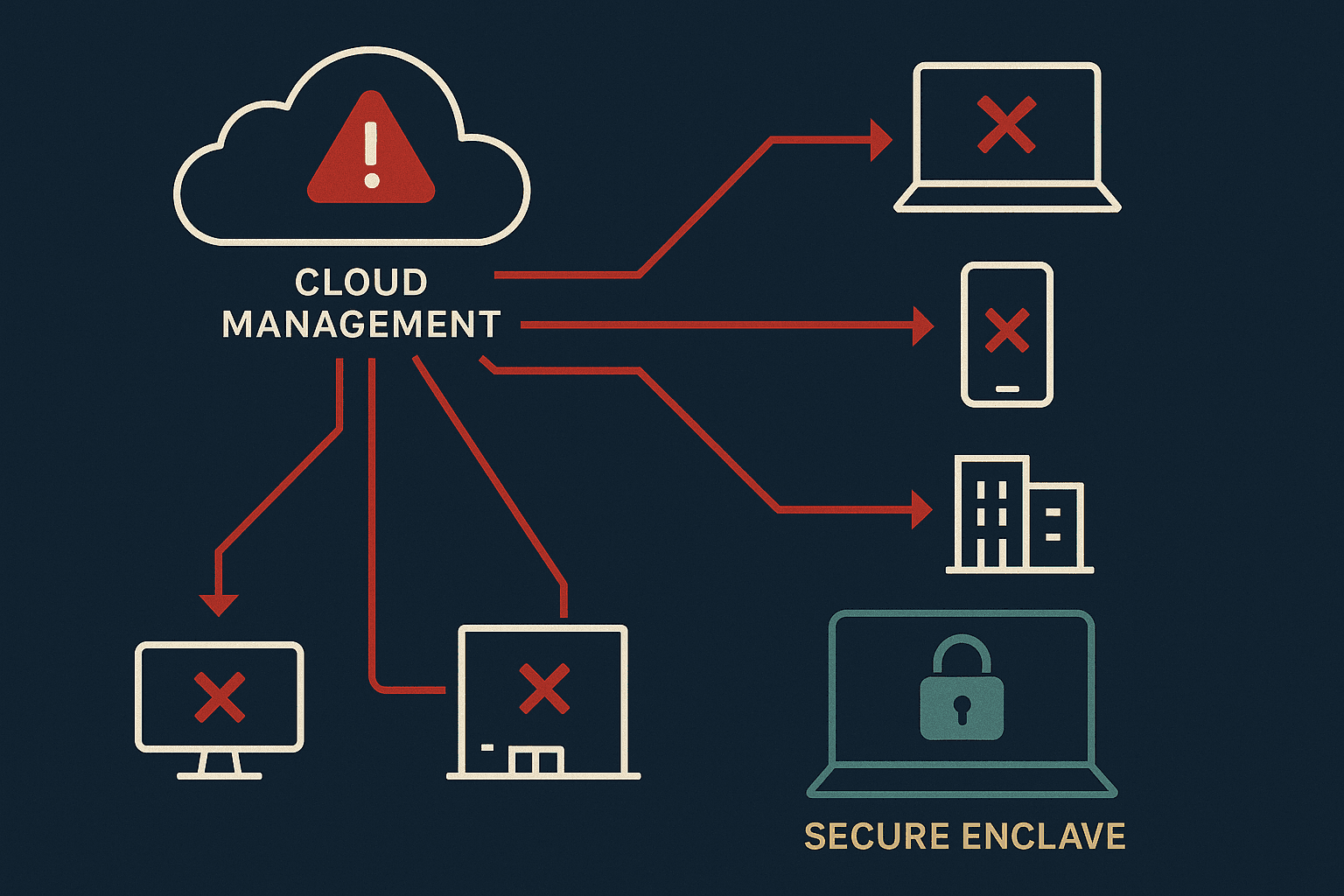
Analysis of the Iran-backed Stryker wiper attack and why offline-first, hardware-secured storage protects against centralized device management compromise.
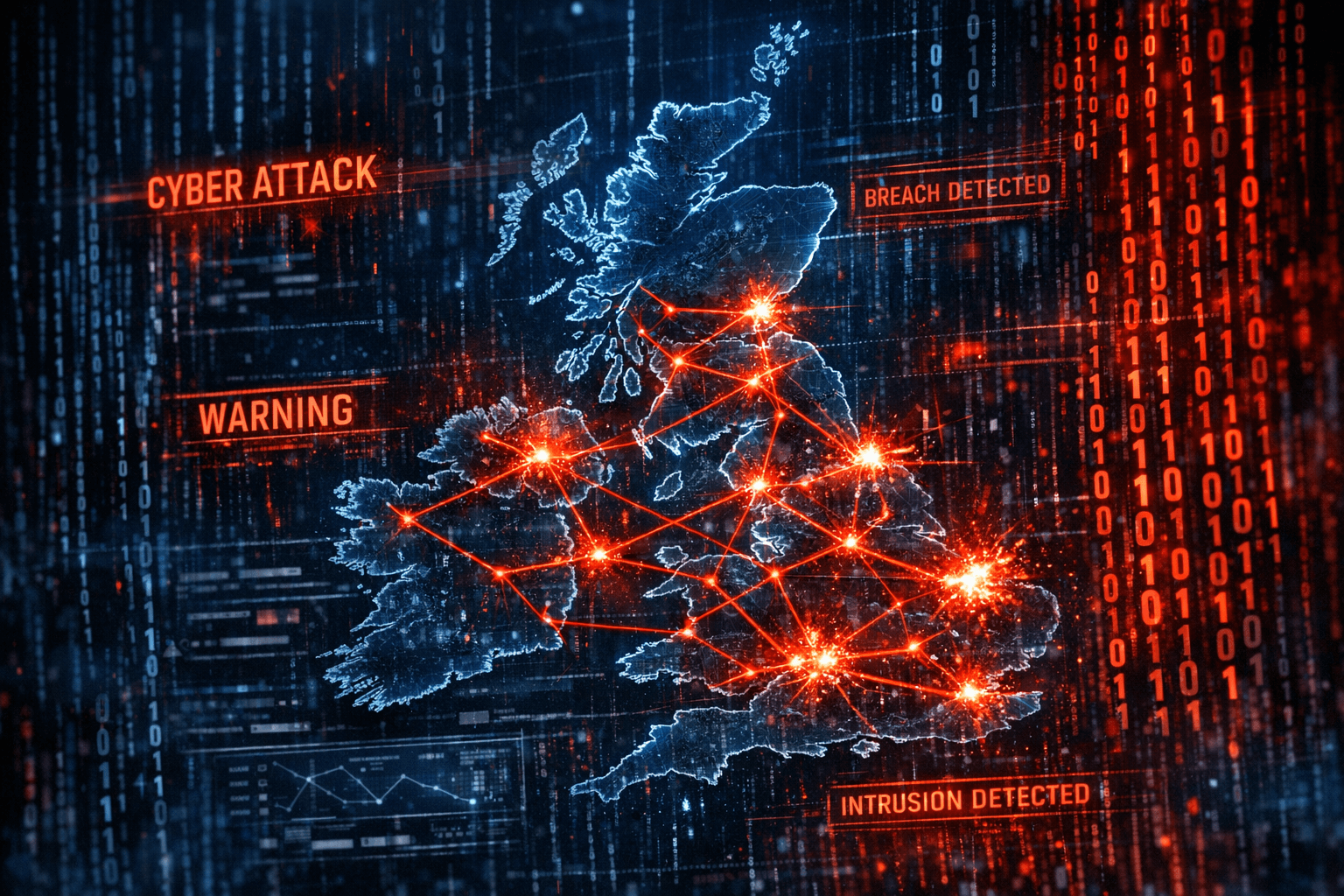
The UK government issued urgent warnings about ongoing Russian hacktivist attacks. Here's what happened, who's at risk, and how to protect your data.

A Duress Code opens a decoy vault while silently destroying your real data when you're forced to unlock under coercion. Here's how it works.
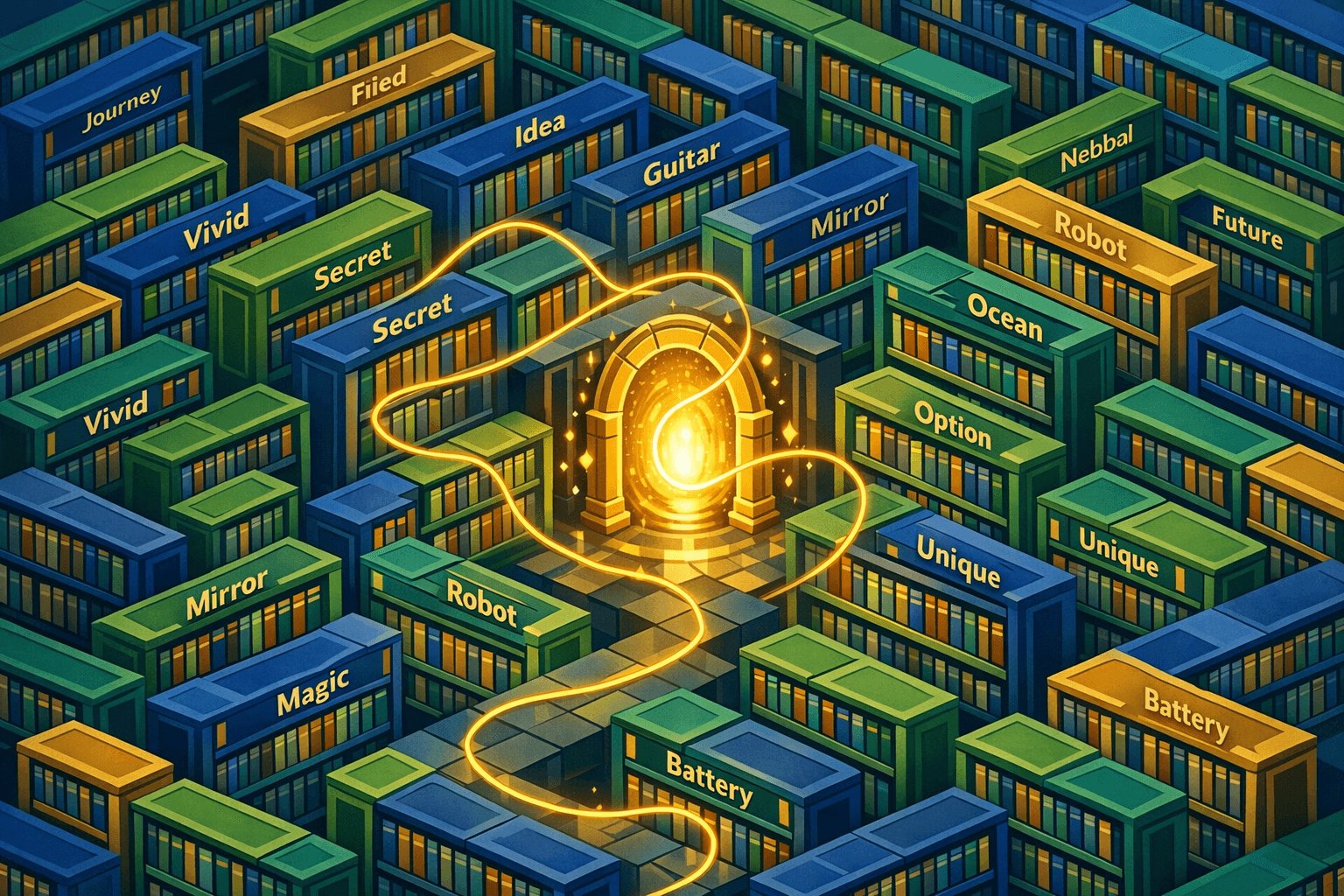
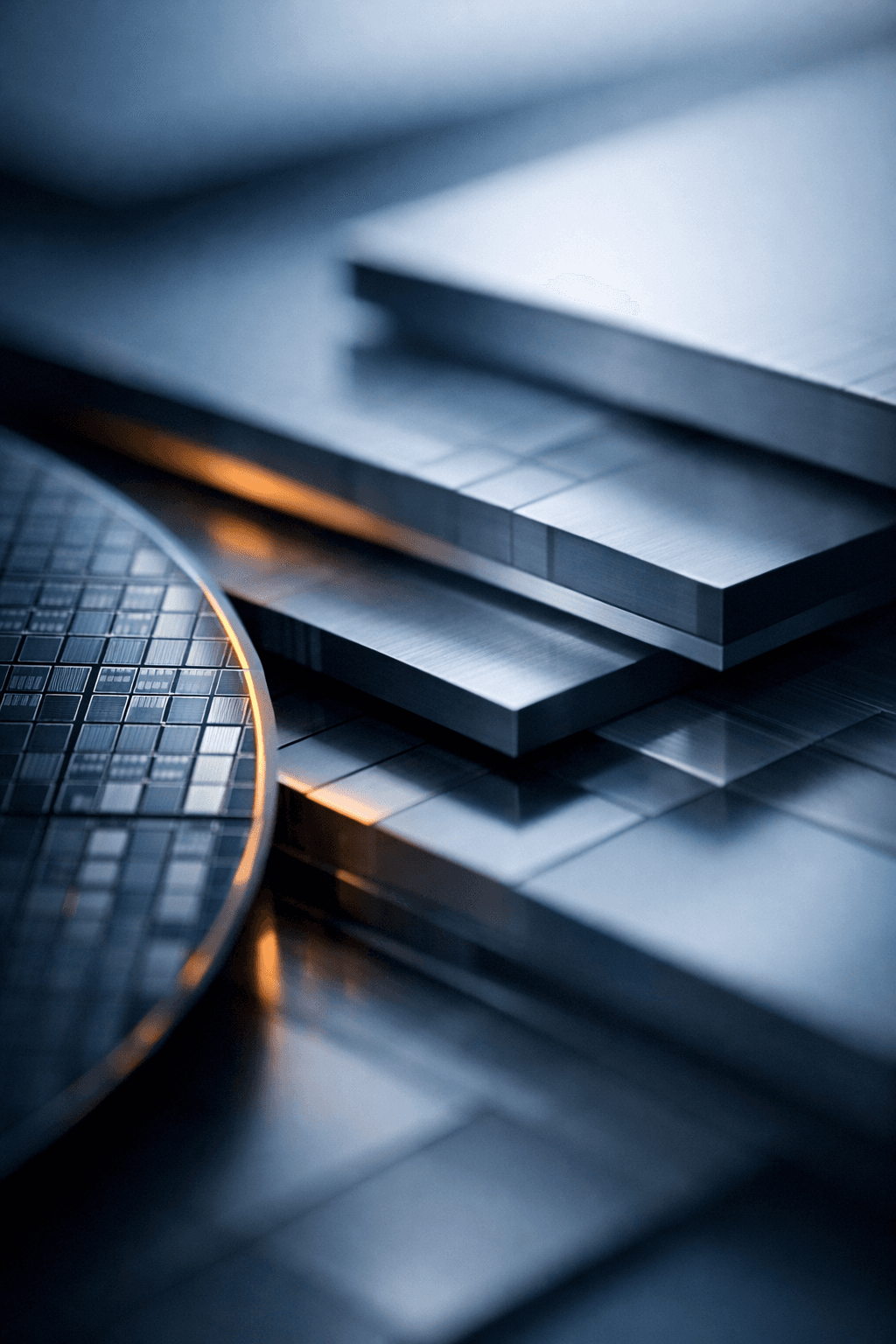
A technical deep-dive into BIP-39, the standard that converts cryptographic keys into memorable seed phrases for cryptocurrency wallets.
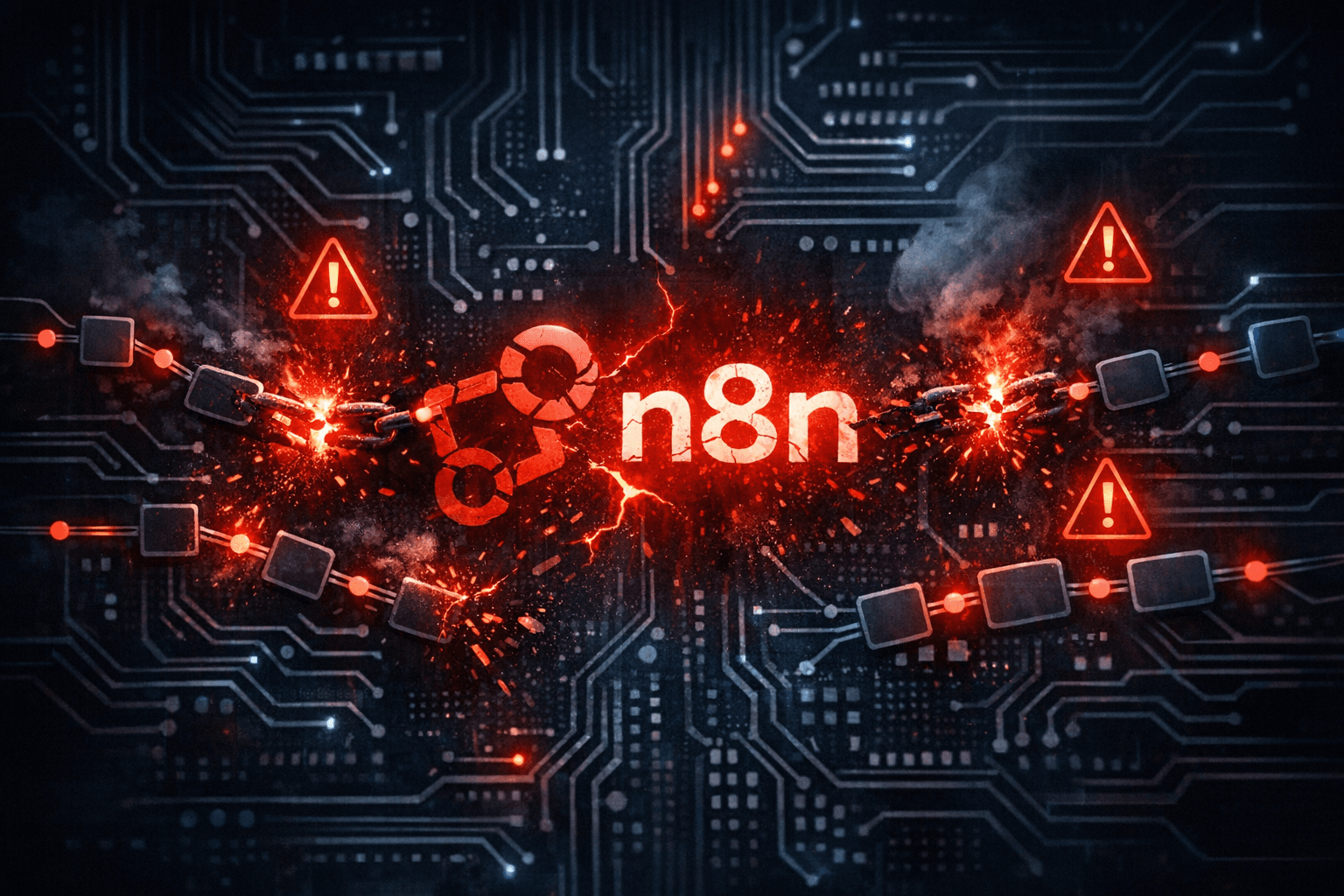
The Ni8mare vulnerability exposed nearly 60,000 n8n workflow automation instances to complete takeover. Here's what failed and why hardware-based security matters.

A practical checklist for auditing phone security, from hidden biometric access to message forwarding rules that most security guides miss.
Most encryption keeps keys in software where they can be extracted. Hardware-anchored encryption generates keys inside dedicated silicon that makes extraction physically impossible.

Ledger customer data exposed through Global-e breach. No funds stolen, but names and addresses compromised. What affected users need to know.