When Centralized Control Becomes a Vulnerability: Lessons from the Stryker Wiper Attack
Analysis of the Iran-backed Stryker wiper attack and why offline-first, hardware-secured storage protects against centralized device management compromise.
When Infrastructure Becomes a Weapon: The Stryker Attack and the Limits of Centralized Control
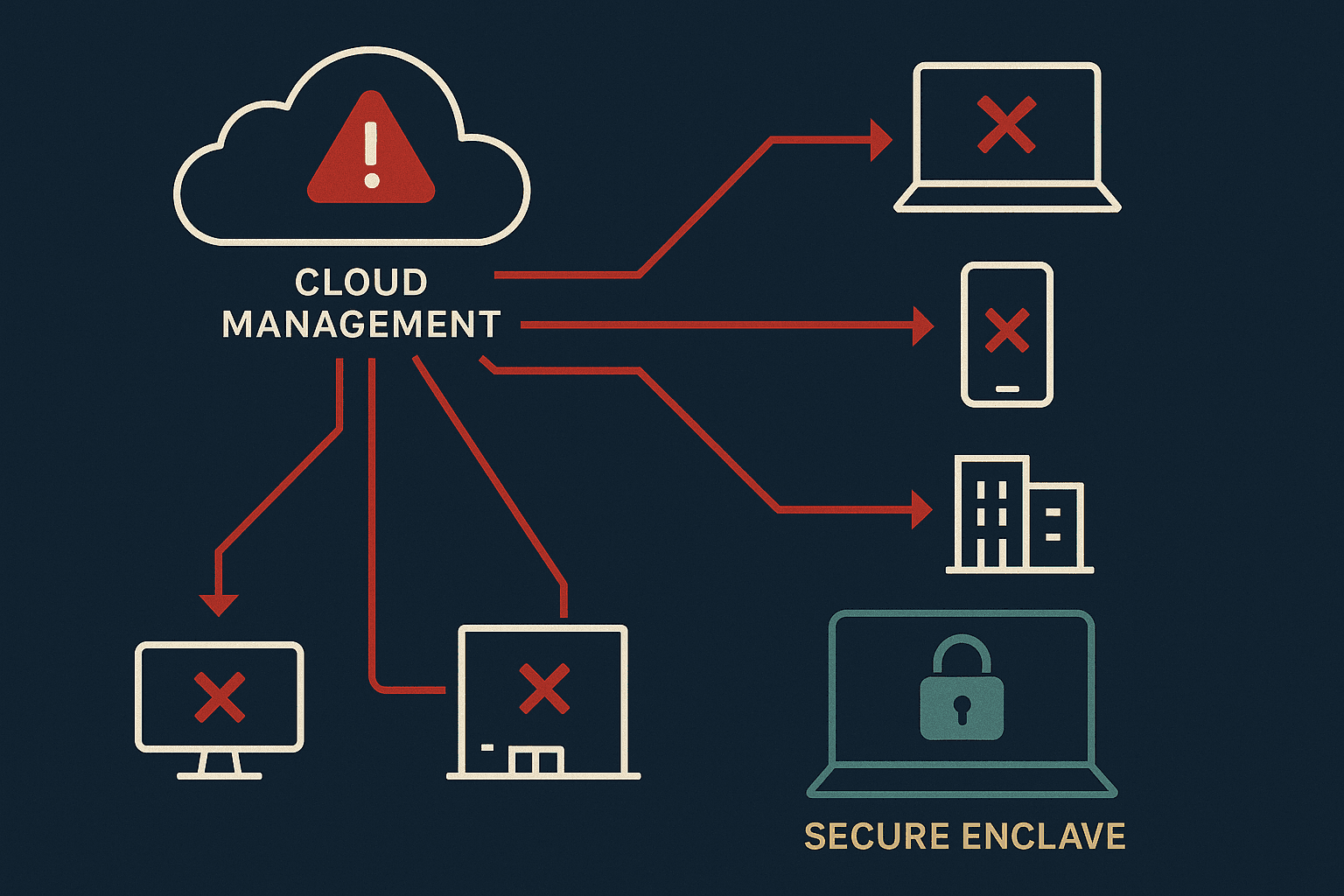
Iran-linked hacktivist group Handala has claimed responsibility for a destructive wiper attack against Stryker, a $25 billion medical device manufacturer, allegedly erasing data across more than 200,000 systems and forcing office shutdowns in 79 countries. The attack appears to have exploited Microsoft Intune, the company's centralized mobile device management system, to issue remote wipe commands across connected infrastructure. The operation disrupted surgical supply chains across U.S. hospitals and exemplifies how dependence on networked, cloud-managed security infrastructure creates catastrophic single-points-of-failure for organizations handling critical services.
This incident reveals a fundamental architectural tension in modern enterprise security. As organizations centralize device management, data governance, and authentication through cloud platforms—reasoning that centralization improves control—they inadvertently construct kill switches that adversaries can turn against them. The Stryker case demonstrates that even for organizations with substantial resources and security teams, compromise of administrative credentials or infrastructure access translates directly into organization-wide destruction.
The Attack Surface: How Intune Became a Wiper
Intune operates as a single administrative console for enforcing security policies across an organization's device fleet. When properly secured, this centralization should prevent data loss. When compromised, it becomes precisely the opposite—a distributed mechanism for simultaneous, coordinated destruction.
The attacker's methodology appears conventional: obtain administrative credentials through initial access techniques, traverse network boundaries, and escalate to administrative systems. Once inside Intune's administrative interface, the attacker issued a "remote wipe" command that formatted connected devices regardless of location or network status. This command executed against mobile devices, laptops, and servers worldwide, constrained only by device connectivity and Intune agent status.
What makes this attack significant isn't technical sophistication but operational scale and consequence. A wiper attack against a manufacturing or retail business destroys inventory records and operational data—costly but recoverable through backups and business interruption insurance. A wiper attack against a medical device supply chain disrupts surgery scheduling, complicates inventory management, and creates gaps in critical patient care. Hospitals couldn't order supplies. Surgeries were deferred. The attack weaponized dependency.
Handala's framing of Stryker as a "Zionist-rooted corporation" (referencing a 2019 Israeli acquisition) suggests ideological targeting rather than opportunistic access. This distinction matters: nation-state-adjacent groups operate with different goals, timelines, and risk tolerance than financially motivated ransomware operators. They're willing to destroy value rather than extort it. They're willing to maintain presence in networks across months. They're willing to absorb diplomatic consequences. This changes defensive posture requirements.
The Centralization Trap
Enterprise security doctrine has increasingly pushed toward centralized visibility and control. Mobile device management, identity and access management, cloud workload protection, endpoint detection—all funnel through centralized consoles. The rationale is sound: centralized management enables consistent policy enforcement, reduces configuration drift, and creates visibility into heterogeneous environments.
But centralization inverts the risk profile. It trades distributed risk (each device has isolated security posture) for concentrated risk (compromise of the central system affects all devices simultaneously). Organizations accept this trade-off because they believe they can defend the central system better than they can defend thousands of endpoints. This is often true. But "better" doesn't mean "adequately," and the margin of safety can collapse rapidly.
Intune requires administrative credentials to access remotely wipe functionality. Those credentials can be obtained through credential stuffing, phishing, SIM swapping attacks on MFA, or exploitation of unpatched vulnerabilities in exposed administrative interfaces. Once obtained, an attacker with valid credentials looks operationally identical to a legitimate administrator. Detection becomes a forensic problem rather than a preventive one.
Stryker presumably invested in monitoring, log aggregation, and security operations. But the destructive command likely executed and completed before humans could respond. Wiper attacks don't establish persistence or exfiltrate data in ways that trigger automated alarms. They format disks. This happens fast.
What Offline-First Architecture Actually Protects Against
This is the architectural problem UltraLocked's design philosophy directly addresses. An offline-first model—where files remain encrypted locally and remain accessible without network connectivity—cannot be remotely wiped by cloud service compromise.
Consider the Stryker scenario through UltraLocked's threat model. If Stryker employees stored sensitive medical data, intellectual property, or correspondence in a hardware-secured vault with offline-first architecture, that data wouldn't live in Intune or any cloud management system. It wouldn't be indexed by the remote wipe command. The encrypted file vault on a device remains functional even if Intune is compromised, even if the network is severed, even if cloud-based admin panels are weaponized.
This isn't theoretical. Organizations handling sensitive data—medical research firms, law practices, government contractors—routinely store the most valuable or risky information on air-gapped or partially-connected devices specifically to prevent network compromise from translating into total data loss. The principle is old: reduce attack surface by minimizing network dependency.
Hardware-secured architecture (leveraging Apple's Secure Enclave) adds a second layer of protection. Encryption keys never exist in software-accessible memory. A compromised operating system or administrative interface cannot decrypt files without cryptographic operations performed inside the Secure Enclave itself. This is meaningful protection against both remote wipe attacks and against sophisticated adversaries who obtain device access but lack Secure Enclave-level privileges.
The offline-first approach also reduces the surface area available for targeting. Intune's attack surface includes credential management, network protocols, cloud storage integration, and administrative console functionality. An offline-first file vault's surface area is substantially narrower: device storage, local encryption, and user authentication. Fewer networked services means fewer compromise vectors.
Practical Implications for Organizations and Individuals
The Stryker attack should prompt organizations to reconsider how they compartmentalize sensitive information. Not all data should flow through centralized management systems. Critical data—intellectual property, research data, medical records, legal documents—benefits from segregation.
For individuals working with medical organizations, legal practices, or government agencies, the lesson is sharper: centralized mobile device management systems should never be the sole protective mechanism for sensitive files. A separate, offline-capable encrypted vault provides genuine isolation. If the device is enrolled in Intune and that enrollment is compromised, files in a hardware-secured vault remain inaccessible to remote wipe commands. The data persists.
This approach requires discipline. Users must differentiate between data that should synchronize across devices for convenience and data that should remain isolated for protection. Synchronization increases accessibility but increases risk. Isolation increases security but reduces convenience. The tradeoff is intentional and explicit.
Emergency protocols matter in high-stakes scenarios. If a user suspects device compromise or faces direct threats, the ability to immediately wipe a device while preserving sensitive data in a separately-secured vault prevents total loss of control. The data in the vault persists. The rest of the device can be reset without consequence. This is particularly valuable for individuals whose threat model includes sophisticated adversaries or nation-state actors.
The Broader Context: Infrastructure as a Weapon
The Stryker attack occurred in a geopolitical context of escalating cyber-physical damage. Nation-state and nation-state-adjacent actors have moved from espionage and disruption toward destruction. Wiper attacks against Saudi electrical infrastructure, Kuwaiti oil facilities, and now medical device supply chains represent a shift in operational goals. Data is destroyed not for ransom but for political messaging and strategic disruption.
This context affects organizational threat modeling. Ransomware defenders focus on backups, immutable copies, and isolated recovery infrastructure. Those defenses don't prevent wipers because wipers don't encrypt—they destroy. Backup systems matter, but they're insufficient. Defense-in-depth requires preventing initial compromise, compartmentalizing data so compromise doesn't spread uniformly, and maintaining offline-capable systems that function even if networked infrastructure fails.
For individuals whose threat model includes sophisticated adversaries, the implications are clear. Depend on centralized cloud systems for daily convenience—backup, synchronization, collaboration—but maintain segregated, offline-capable secure storage for information that demands higher assurance. Hardware-secured vaults with offline-first architecture serve that purpose. The data they protect survives network compromise, remains functional during outages, and remains accessible to authorized users even when centralized services fail.
The Stryker incident is significant because it demonstrates that scale and resources don't guarantee protection against determined adversaries who control the right compromises. Better to design systems that don't require perfect defense of centralized infrastructure, because centralized infrastructure, by definition, is a high-value target.
Organizations and individuals should segregate accordingly. Not all data follows the same risk profile. Not all data should depend on the same protective infrastructure. Hardware-secured, offline-capable storage for the most sensitive information represents a different architectural approach—one that has become increasingly relevant as centralized systems become increasingly attractive targets.